The threat landscape in 2026 looks nothing like it did five years ago. The amateur hackers with clunky ransomware are largely gone. What replaced them is something far more concerning: professional criminal organisations running malware like a subscription software business, complete with helpdesks for affiliates, automated deployment, and AI tools that generate convincing phishing lures at industrial scale.
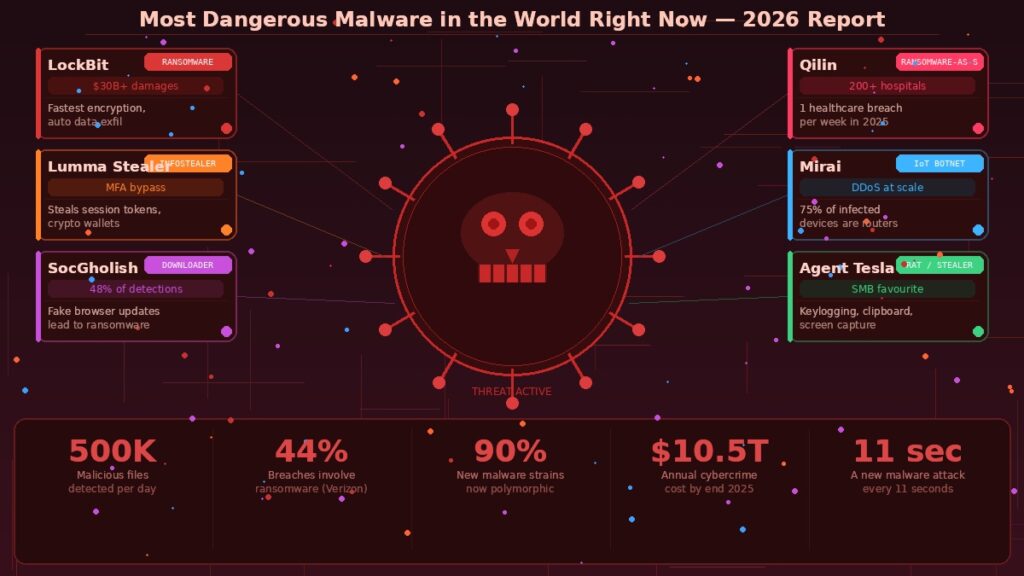
Kaspersky’s sensors now detect around 500,000 malicious files per day — 7% more than the previous year. A new malware-based attack lands somewhere in the world every 11 seconds. Global cybercrime costs are on track to reach $10.5 trillion by the end of 2025. These aren’t theoretical risks. They’re the daily operating conditions of the internet.
Here are the threats that security teams are most concerned about right now.
LockBit — The Ransomware Machine
LockBit remains the most prolific ransomware operation in history, responsible for more confirmed attacks than any other group. Even after a major international law enforcement takedown in 2024, the operation rebuilt and resumed campaigns within weeks — a demonstration of how resilient these criminal enterprises have become. Its model is pure efficiency: stolen credentials buy access, automated tools handle lateral movement, and encryption locks the victim out within hours. The group’s leak site applies simultaneous pressure — pay up, or your data goes public. Global ransomware damages surpassed $30 billion in 2023 and have continued rising.
Lumma Stealer — The MFA Bypass Specialist
What makes Lumma Stealer particularly dangerous is what it targets: not passwords, but session tokens and browser cookies. By stealing these, attackers can bypass multi-factor authentication entirely and log in as if they’re already a verified user. It also extracts crypto wallet credentials, saved passwords, and autofill data. Microsoft took down a significant portion of Lumma’s infrastructure in mid-2025 — and it was back within days, using fake software installers and “ClickFix” phishing pages that trick users into running malicious commands themselves. It’s now one of the core enablers of the wider ransomware ecosystem, supplying stolen access to groups like Qilin and Akira.
SocGholish — The Gateway Nobody Notices
SocGholish has led the top 10 malware charts for seven consecutive quarters, accounting for nearly 48% of all detections tracked by the Centre for Internet Security. Its method is deceptively simple: it hides inside compromised legitimate websites and presents visitors with a convincing fake browser update prompt. Click it, and you’ve installed a downloader that quietly opens the door for remote access tools and ransomware. It doesn’t need a zero-day exploit or advanced hacking technique — it needs a moment of inattention from a user who just wants their browser to work.
Qilin — Healthcare’s Worst Nightmare
Qilin topped OpenText’s 2025 nastiest malware list for good reason: it executed more than 200 confirmed incidents, with an average of one new healthcare breach per week throughout the year. Hospitals, laboratories, and local governments were its primary targets. Qilin operates as a Ransomware-as-a-Service platform with ties to state-backed actors, and its “Call Lawyer” negotiation feature signals how professionalised these operations have become. When a hospital’s systems go down, patients can’t access records, operations get cancelled, and ambulances get diverted. The human cost of Qilin’s campaigns extends well beyond the ransom figures.
Mirai — The IoT Botnet That Won’t Die
Mirai was first identified in 2016. It’s still running campaigns in 2026. Mirai targets Internet of Things devices — routers, smart cameras, baby monitors, smart speakers — and enslaves them into botnets for distributed denial-of-service attacks that can knock entire websites and services offline. Roughly 75% of Mirai-infected devices are routers. IoT devices are a persistent weak point because they typically lack the storage or processing power for robust security software, default passwords are often left unchanged, and users rarely think to patch them. As the number of connected devices grows toward 75 billion, Mirai’s attack surface grows with it.
Agent Tesla — The Small Business Stalker
Agent Tesla has been active since 2014 and remains one of the most consistently deployed credential stealers in the world. It’s particularly prevalent against small and mid-sized businesses, delivered through phishing emails disguised as invoices and purchase orders. Once installed, it runs silently — logging keystrokes, capturing clipboard content, taking periodic screenshots, and exfiltrating everything over common protocols that don’t trip basic security filters. The damage tends to be financial fraud and account takeover rather than the dramatic operational shutdowns of ransomware, but the impact on smaller businesses without dedicated security teams can be just as devastating.
The Bigger Shift: Malware Has Gone Professional
Perhaps the most significant development in 2026 is structural rather than technical. The Malware-as-a-Service market on the dark web expanded by 30% last year, meaning entry-level criminals can now rent sophisticated malware, infrastructure, and support for a monthly fee. Nearly 90% of new malware strains are now polymorphic — they change their underlying code structure every time they execute to evade signature-based detection. And 45% of malware now hides inside encrypted web traffic, invisible to traditional firewalls.
The defences that worked five years ago — basic antivirus, a perimeter firewall, and telling staff not to click suspicious links — are not sufficient against an ecosystem this professional and this automated. The minimum viable defence in 2026 includes endpoint detection and response tools, phishing-resistant multi-factor authentication, network segmentation, and regular offline backups. Not as best practice. As baseline.